Usage, Privacy & Disclaimer
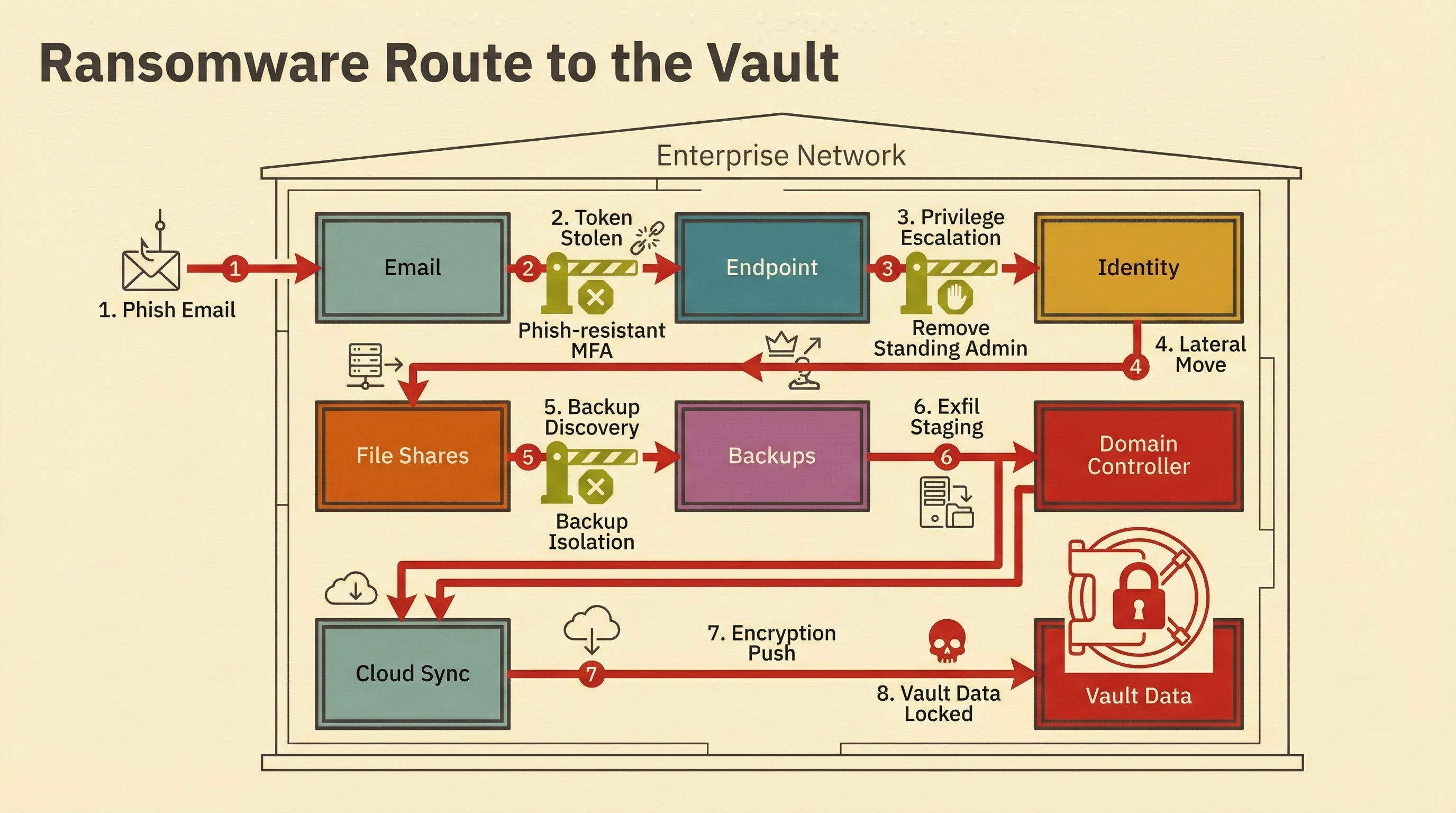
This report is intended for informational and defensive security purposes. The content describes attack patterns to help defenders reduce risk. It does not provide operational instructions for harm. Redistribution is permitted with attribution to Rocheston Zelfire Intelligence.
All telemetry and incident patterns are anonymized and aggregated. No customer identifiers are included. Where examples are described, details are generalized to prevent attribution. Individual organizations cannot be reverse-identified from any data in this report.
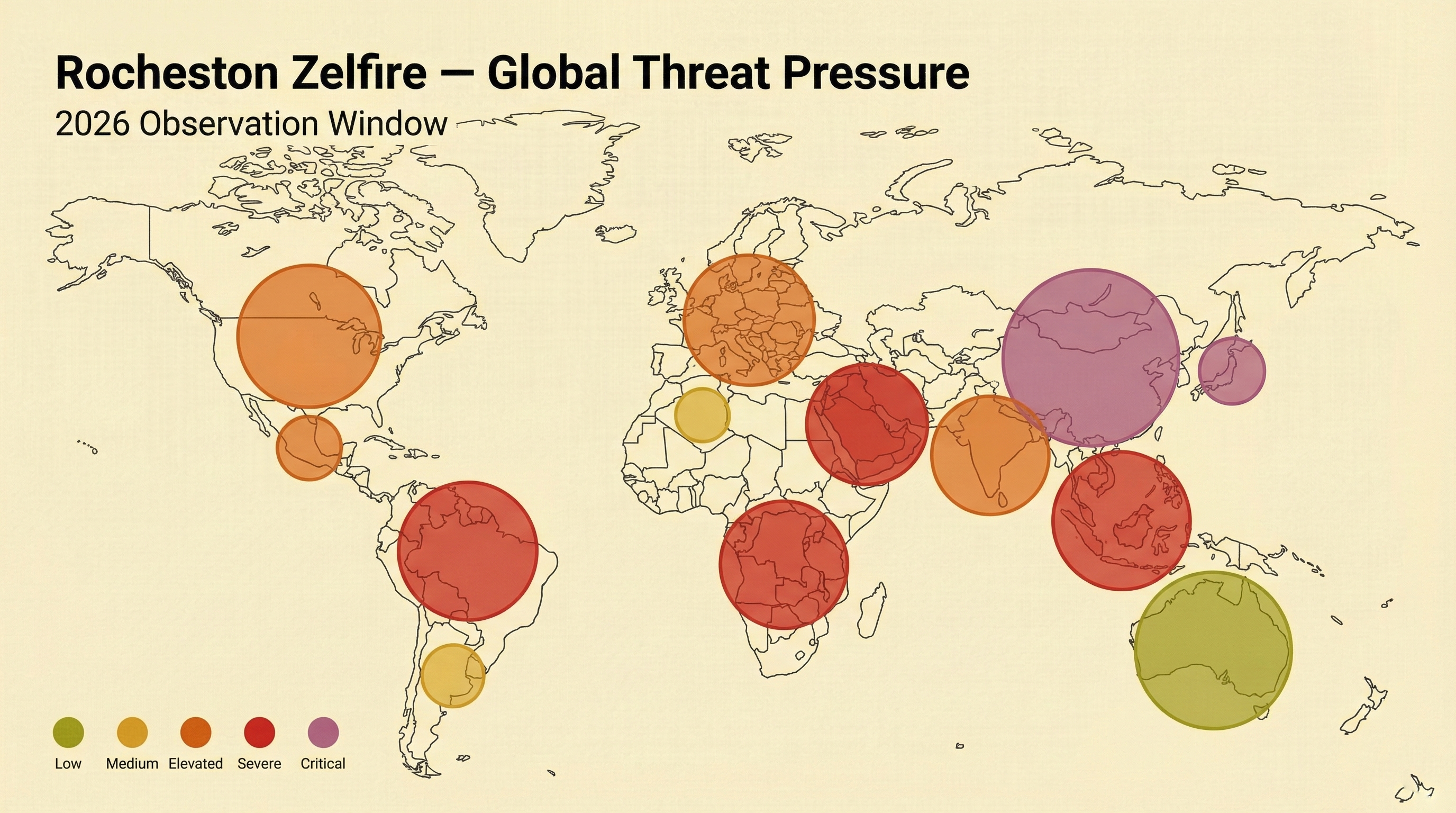
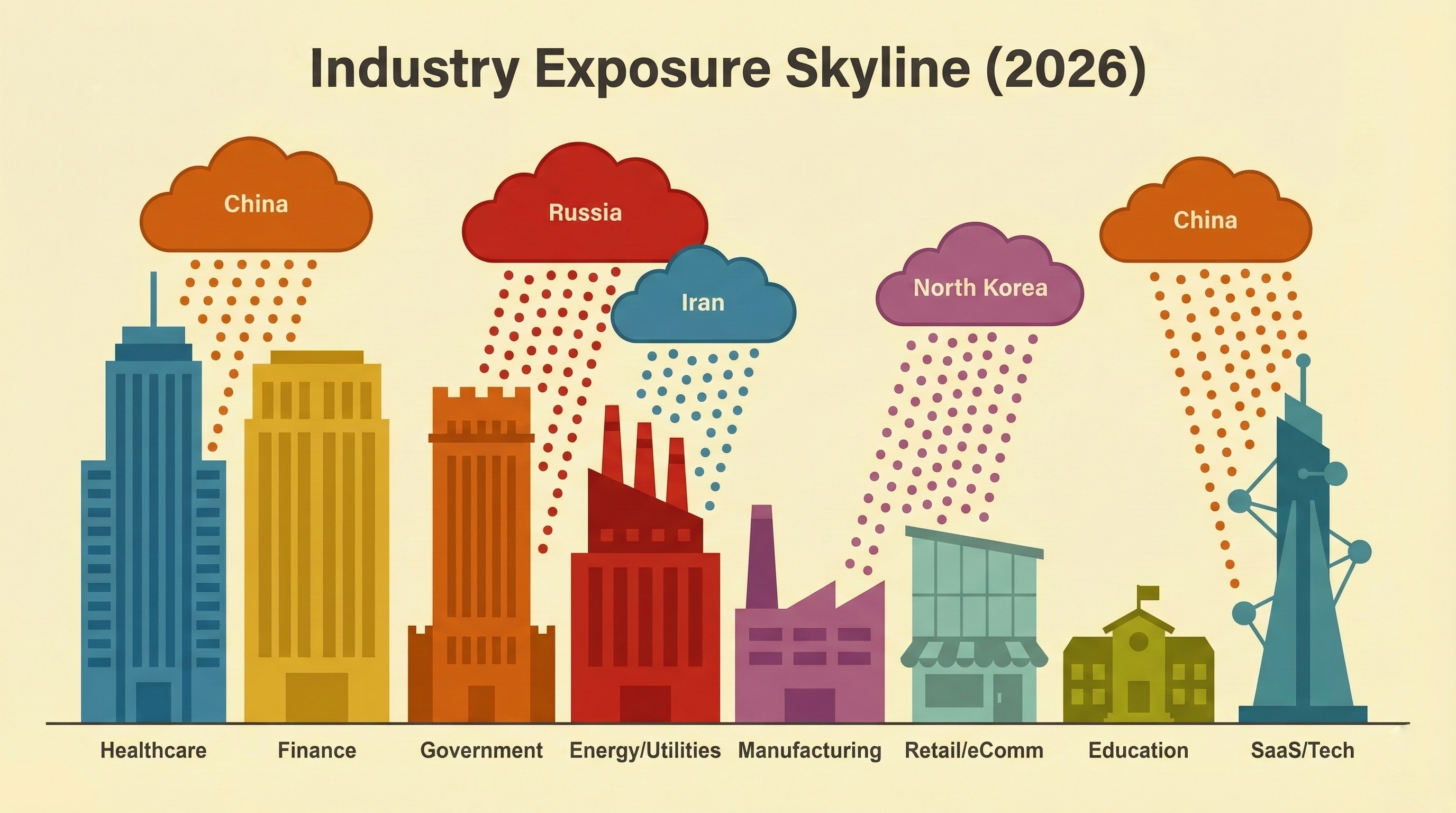
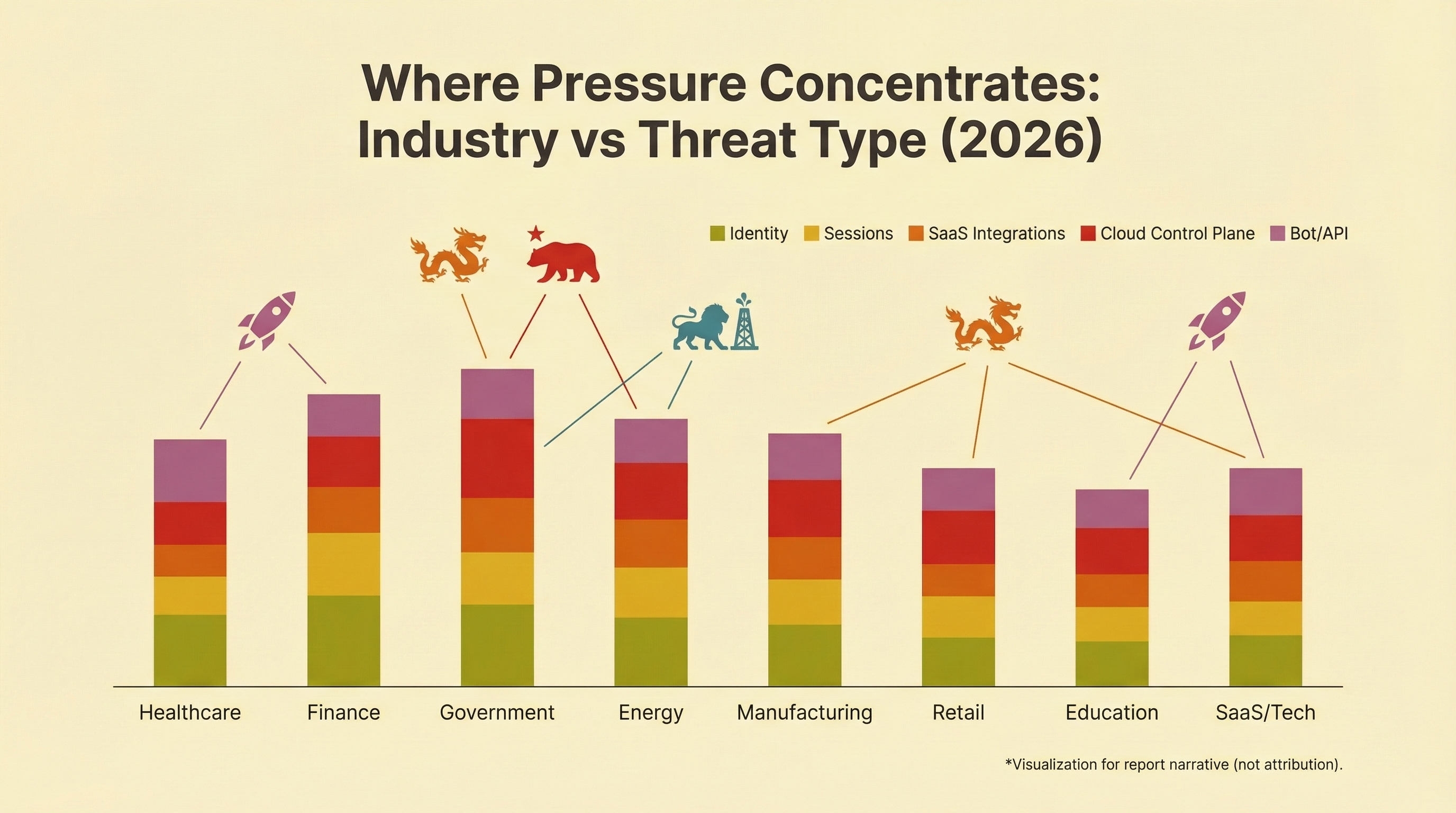
Primary analysis window: last 12 months (rolling), with references to multi-year baseline trends where relevant. Incident data reflects patterns observed across opt-in telemetry sources during the 2025–2026 period.
Findings reflect patterns across enterprise environments. Smaller organizations may experience different threat mixes. All statistics are directional; precise figures depend on environment, sector, and maturity level.
This report is provided as-is. Rocheston Zelfire makes no warranties about completeness or fitness for a specific purpose. Security guidance should be applied in context with qualified practitioners.
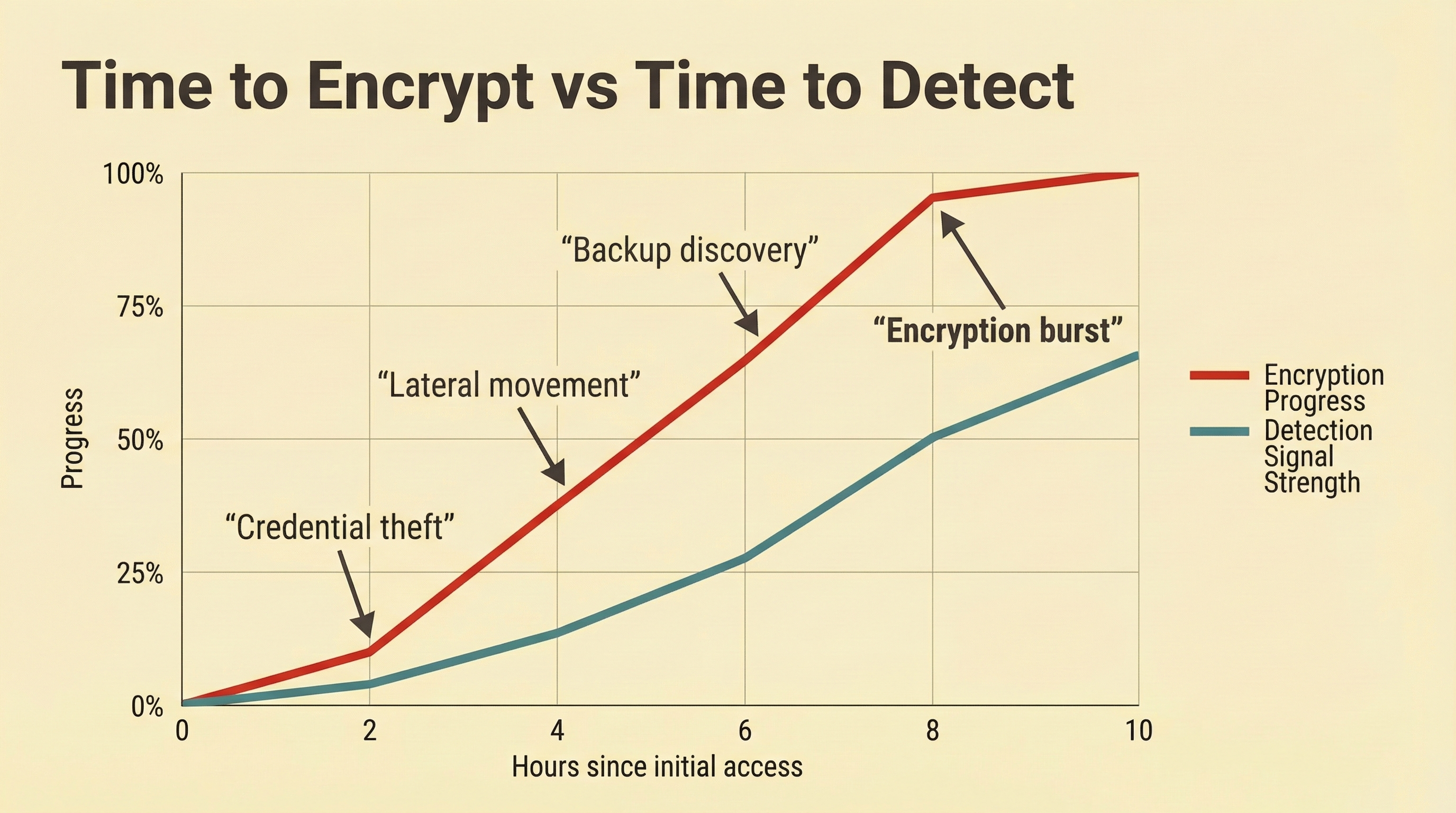
Findings are based on aggregated telemetry across participating environments. Stronger monitoring may produce more signals than limited instrumentation.
Threat activity evolves continuously. Observations reflect the analysis window and may shift as attacker techniques adapt.
Findings should be interpreted alongside industry, architecture, and monitoring maturity, which influence exposure and detection.